Operation Wolf
Recently RetroGamer ran a feature on Operation Wolf (Taito, 1987) that mentioned the emulation in M.A.M.E. and the ‘arcade perfect’ Taito Legends (PS2, 2005) was not quite correct – missing cutscenes, a missing boss, some other details. Unfortunately, that’s true – the reason is Operation Wolf contains copy protection that has never been properly emulated. I was the programmer who implemented the protection emulation on Taito Legends (PS2) and then M.A.M.E. and it’s actually based on a bootleg (pirate) version of the game. The problem was that original ‘cracker’ of the game didn’t get everything right. The protection device is actually an 8 bit micro controller of some sort that maps into 256 bytes of the main CPU address space. It runs a private embedded program that cannot be read out, so what exactly the controller does is somewhat of a mystery. Memory mapping is a very effective copy protection when done right, as the main CPU can just write bytes into random locations, and then expect certain results & logic back at a later date without any obvious link as to what inputs caused what outputs. The bootleg sheds light on the setup though – one example is the end of level detection – the main cpu constantly writes the number of enemies, tanks & helicopters remaining in the level into shared memory. Only when all of these are zero does the protection chip write a byte that signals ‘level is complete’. The protection is effective because without a reference it’s very hard to know the internal logic of the controller.
Prototype
By chance, a prototype Japanese version of Operation Wolf was recently discovered – this was almost certainly a test unit placed on location for player feedback before the game was finished, and before the copy protection was added. It’s fairly close to the final game though, and does contain the missing scenes and boss, so in theory it should be possible to compare the two programs, and make a guess at what the protection logic is doing compared to the unprotected reference program. I thought some people might like to read about this process, so hence this post – be warned, it’s going to get a bit technical…
Initial Comparison
In an ideal world the two games would disassemble to near identical programs, with the only difference being a bit of protection logic replacing the original game logic from the prototype. Unfortunately that’s not the case – what we can see is that there is a lot of code that is logically the same – but it’s assembled to different locations, and variables have moved around in memory. Some of that is deliberate – with some variables moving into shared c-chip (protection) ram rather than main memory, but some of it is clearly just from sections being moved around in the original source and the assembler following suit.
| 00541E: 6100 0024 bsr $5444 005422: 3211 move.w (A1), D1 005424: 0241 8200 andi.w #$8200, D1 005428: 0C41 8000 cmpi.w #-$8000, D1 00542C: 660E bne $543c 00542E: 4251 clr.w (A1) 005430: 7200 moveq #$0, D1 005432: 1229 001F move.b ($1f,A1), D1 005436: 3F01 move.w D1, -(A7) 005438: 4E42 trap #$2 00543A: 548F addq.l #2, A7 00543C: D2C4 adda.w D4, A1 00543E: 51C8 FFE2 dbra D0, $5422 005442: 4E75 rts | 006100: 6100 002C bsr $612e 006104: 3211 move.w (A1), D1 006106: 0241 8200 andi.w #$8200, D1 00610A: 0C41 8000 cmpi.w #-$8000, D1 00610E: 6616 bne $6126 006110: 48E7 8000 movem.l D0, -(A7) 006114: 4251 clr.w (A1) 006116: 7200 moveq #$0, D1 006118: 1229 001F move.b ($1f,A1), D1 00611C: 3F01 move.w D1, -(A7) 00611E: 4E42 trap #$2 006120: 548F addq.l #2, A7 006122: 4CDF 0001 movem.l (A7)+, D0 006126: D2C4 adda.w D4, A1 006128: 51C8 FFDA dbra D0, $6104 00612C: 4E75 rts |
| 0119F8: 203C 4001 0306 move.l #$40010306, D0 0119FE: 3439 000F F036 move.w $ff036.l, D2 // current level 011A04: 0C02 0002 cmpi.b #$2, D2 011A08: 6700 0004 beq $11a0e 011A0C: 7000 moveq #$0, D0 011A0E: 3439 000F F04C move.w $ff04c.l, D2 011A14: 0242 00FF andi.w #$ff, D2 011A18: 08E9 0003 0000 bset #$3, ($0,A1) 011A1E: D5FC 0000 0010 adda.l #$10, A2 011A24: 6100 E5B8 bsr $ffde 011A28: 4E75 rts | 00DD8C: 203C 4001 0306 move.l #$40010306, D0 00DD92: 0C6D 0002 0B20 cmpi.w #$2, ($b20,A5) 00DD98: 6700 0004 beq $dd9e 00DD9C: 7000 moveq #$0, D0 00DD9E: 142D 0C7D move.b ($c7d,A5), D2 00DDA2: 08E9 0003 0000 bset #$3, ($0,A1) 00DDA8: D5FC 0000 0010 adda.l #$10, A2 00DDAE: 6100 E834 bsr $c5e4 00DDB2: 4E75 rts |
In the above tables the code functionally does the same thing but you can see it’s assembled to different addresses. The original code (on the left) accesses the 8 bit c-chip shared ram for the level variable ($ffxxx), so it’s changed to byte instructions rather than word.
Software Architecture
Operation Wolf has interesting software architecture. Unlike most games of this
era which have a simple main loop and linear code flow, Operation Wolf
implements a co-operative threading model where routines run in 68K user mode
until giving up their timeslice and a supervisor mode scheduler picks the next
thread to run. There are 32 thread slots, and each enemy in game run as its
own thread/object as well as a thread for coins, scrolling the level, level
specific gameplay and so on. The code is very robust when creating threads,
for example if there are no free slots, the creating thread just spins until
a slot frees up. The rest of the game just keeps on playing in the background.
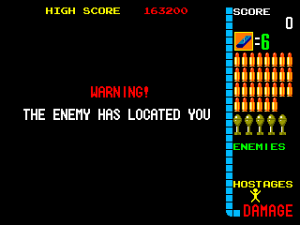
Another interesting detail is that a thread can give up it’s timeslice for more
than 1 frame – this makes it really easy to implement timed events. The ‘WARNING’
text at the end of level 2 is handled by a thread that prints to screen, then just
waits a second before spawning the boss enemy thread.
Each level in the game implements its own logic thread and often sub-threads -
this is the major difference between the protected game and the bootleg – the bootleg
mostly implements the parts that are generic between all levels rather than all of
the details. The biggest single area the bootleg did not implement revolves
around location 0x5f in the shared c-chip RAM. The original code sets up a thread
that just waits for this value to become non-zero. It then jumps to a set of
functions defined in a look-up table (that can then spawn further threads). There
are 10 non-null functions tied to this routine.
1: Enemy spawn for level 7 (first ‘Located’ cut-scene)
2: Enemy spawn for level 8 (second ‘Located’ cut-scene) – zoom in helicopters
3: Enemy spawn for level 9 (third ‘Located’ cut-scene)
4: Boss & hostage sequence for level 2
5: Enemy spawn when less than 45 enemies in level 2 (paratrooper drop-down)
6: Enemy spawn when less than 25 enemies in level 2
7: Enemy spawn when 0 men left in levels 2,4,5,6
8: Enemy spawn when 0 men left in level 3
9: Enemy spawn when 0 men left in level 1
10: Special explosion animation when level 4 (Powder Dump) is completed
The bootleg also misses some other details, for example in level 5 the c-chip
sets a flag when all men are destroyed (not vehicles) and this triggers the 68K
to scroll the screen vertically to focus on the remaining helicopter enemies.
The ‘Enemy has located you’ cut-scenes appear ‘randomly’ between levels in the
original game, but are deliberately disabled in the bootleg. The exact formula
for determining if the cut-scene appears is ‘(frameCount & levelNumber)==0′. There are three different cutscene levels.
Source Dumps
Should you want to see what the code for an old arcade game looks like I’ve attached my annotated dumps of the original and prototype source code – it fills in some labels and some variables and the thread functions to make it easier to read!
_signal_end_of_level: 0053EC: 322D 0B20 move.w $CURRENT_LEVEL, D1 0053F0: 0C41 0006 cmpi.w #$6, D1 0053F4: 6614 bne $540a 0053F6: 1B7C 0001 0998 move.b #$1, ($998,A5) 0053FC: 4EB9 0000 3314 jsr $3314.l 005402: 3F3C 0020 move.w #$20, -(A7) 005406: 4E46 trap #$6 (SLEEP_THREAD_FOR_N_FRAMES) 005408: 548F addq.l #2, A7 00540A: 6100 0012 bsr $541e 00540E: 3F3C 003C move.w #$3c, -(A7) 005412: 4E46 trap #$6 (SLEEP_THREAD_FOR_N_FRAMES) 005414: 548F addq.l #2, A7 005416: 1B7C 0001 0999 move.b #$1, $END_OF_LEVEL_FLAG 00541C: 4E45 trap #$5 (KILL_THREAD) opwolf.dasm opwolfp.dasm



Thanks for the write up. Interesting to see such a approach to managing multiple npc’s and objects. A clean way to do it.